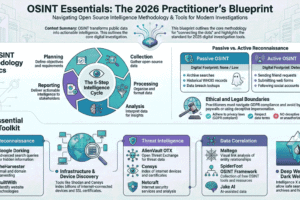
OSINT – Open-Source Intelligence [Maltego]
OSINT – Open-Source Intelligence [Maltego]
OSINT means collecting and gathering information from publicly available sources, like google, Social medias like, Facebook, WhatsApp, telegram, Instagram etc….
Who Uses OSINT?
- National Security & Law Enforcement: For global awareness, threat assessment, and investigations.
- Cybersecurity: To identify vulnerabilities, track malicious actors, and understand emerging threats.
- Businesses: For due diligence, market research, competitive analysis, and risk management.
- Journalists & Researchers: To uncover stories, verify facts, and document events.
Examples of OSINT in Action:
- Cybersecurity: Finding an organization’s unpatched software or leaked credentials by searching public forums and code repositories.
- Threat Intelligence: Monitoring ransomware leak sites and hacker forums to understand new tactics.
- Background Checks: Gathering public social media and professional information about individuals.
Tools used in OSINT
There are multiple tools available for OSINT, which helps investigators to gather information across the digital and physical society.
1. Maltego
This is a tool for data mining and relationship mapping. It’s a Graphical link analysis tool. This transforms data into interactive graphs for investigations.
In this hands-on tutorial, I’ll demonstrate how to use Maltego – a powerful OSINT (Open Source Intelligence) tool – to map a target’s digital footprint using TryHackMe.com as our case study.
Step by step Guide to Map TryHackMe’s Infrastructure
Step 1: Installation & Setup
- Download the Community Edition of Maltego by visiting it’s official website com
- Create an Account during the installation for free
- Open Maltego and create a new graph for our investigation
Step 2: Initial Domain Analysis
- Drag a “Domain” entity onto the Canvas
- Double-Click and enter tryhackme.com
- Right Click a Run Transform a Select “To DNS Name”
Step 3: Explore DNS and Infrastructure
After running the “To DNS Name” transform, Maltego will resolve the domain to associated DNS records. In our investigation of tryhackme.com, we discovered multiple subdomains and related infrastructure. Some of the notable DNS names found include:
- tryhackme.com
- tryhackme.com
- tryhackme.com
- com.cdn.cloudflare.net
- worker-test.tryhackme.com
This reveals TryHackMe’s use of Cloudflare for CDN and DDoS protection, as well as separate subdomains for blogs, help centres, and remote access services.
Step 4: Identify IP Addresses and Geolocation
By transforming DNS names to IP addresses, we uncovered the following IPv4 addresses linked to TryHackMe’s
- 20.29.66
- 66.164.239
These IPs correspond to Cloudflare proxy servers, confirming the use of reverse proxy services to protect origin servers.
Step 5: Extract Email Addresses and Contact Information
Maltego can also uncover email addresses associated with the domain. For TryHackMe, we identified several organizational emails:
- sales@tryhackme.com
- support@tryhackme.com
- hello@tryhackme.com
- qa@tryhackme.com
- stuxnet@tryhackme.com
These emails appear in help articles, legal pages, and community discussions, indicating points of contact for sales, support, quality assurance, and possibly internal development.
Step 6: Map Related URLs and Help Resources
The tool also extracted numerous URLs from the help centre and legal documentation, such as:
- https://help.tryhackme.com/en/articles/6498338-user-tokens
- https://tryhackme.com/pricing
- https://help.tryhackme.com/en/articles/8469856-legal-compliance-requirements
These resources reveal how TryHackMe structures its support and legal documentation, and where users are directed for billing, compliance, and token management.
Step 7: Visualize Relationships with Entity Graphs
Maltego allows us to visualize the connections between entities. Below is a summary of the top linked entities from our scan:
|
Rank |
Entity Type |
Value |
Total Links |
|
1 |
IPv4 Address |
104.20.29.66 |
25 |
|
2 |
Email Address |
sales@tryhackme.com |
9 |
|
3 |
Email Address |
support@tryhackme.com |
7 |
|
4 |
Domain |
tryhackme.com |
6 |
|
5 |
DNS Name |
tryhackme.com |
6 |
📌 For Full Information Visit: https://github.com/FatheenNizam2024/OSINT-Maltego-