🔍 OSINT 101: The Superpower of Open Source Intelligence Your Guide to Becoming a Digital Detective 📝 Blog Post 👋 Hey Future Investigators! Ever wondered how hackers find information about people? Or how journalists uncover hidden truths? Or how companies protect themselves …
𝐈𝐧𝐟𝐨𝐫𝐦𝐚𝐭𝐢𝐨𝐧 𝐢𝐬 𝐞𝐯𝐞𝐫𝐲𝐰𝐡𝐞𝐫𝐞, 𝐛𝐮𝐭 𝐢𝐧𝐭𝐞𝐥𝐥𝐢𝐠𝐞𝐧𝐜𝐞 𝐢𝐬 𝐚 𝐜𝐫𝐚𝐟𝐭. 🕵️♂️💻 In an era of digital information overload, the ability to find, verify, and analyze public data has become a foundational skill for cybersecurity, investigative journalism, and digital forensics. Today, I am …
AWS Security Auditor 🔐 An automated cloud security scanning tool that identifies misconfigurations in AWS environments before they become million-dollar breaches. 🎯 Overview AWS Security Auditor is a Python-based automated security scanning tool designed to identify common misconfigurations in Amazon …
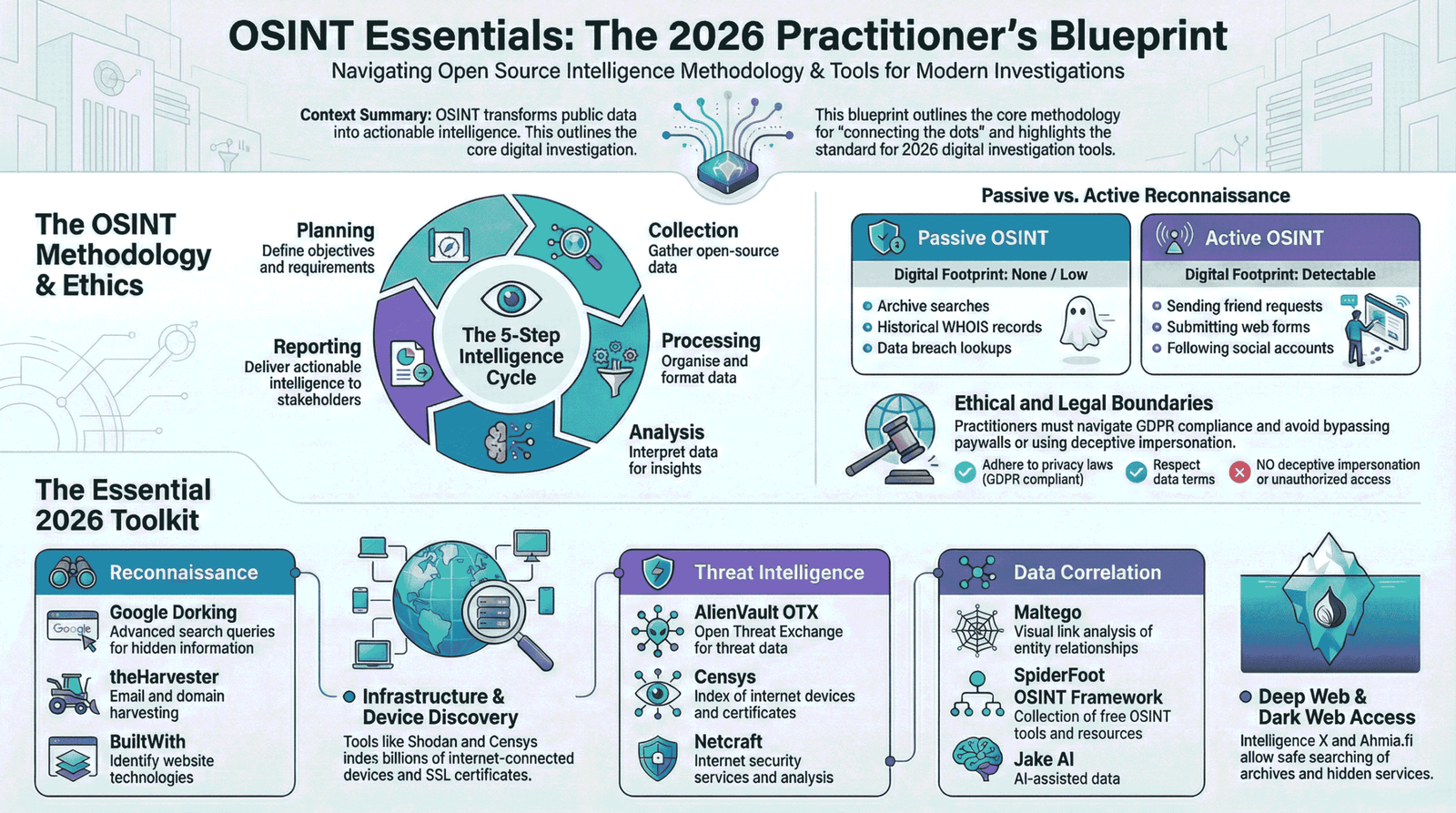
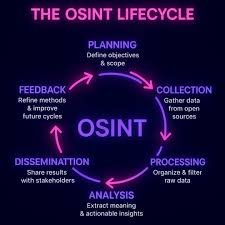
OSINT Open Source Intelligence (OSINT) is the process of collecting and analyzing publicly available information for cybersecurity investigations and research. This article explains OSINT sources, process, legal considerations, and its importance in digital investigations. Tools Covered:Google Dorking, Shodan, Maltego, Have …
Abstract Open-Source Intelligence (OSINT) has become a fundamental component of modern cybersecurity investigations. This article presents a structured overview of ten widely used OSINT tools and examines their relevance for cybersecurity students. The study emphasizes responsible usage, analytical development, and …
Introduction In today’s digital world, information is everywhere. From social media and websites to publicrecords and online forums, massive amounts of data are freely available. The ability to collect,analyze, and use this information effectively is known as OSINT–Open Source Intelligence.OSINT …
In my latest blog post, “OSINT 101,” I break down the workflow professional investigators use to verify and locate images online. This project demonstrates the practical application of:✅ Observation: Using the PLWC (Plates, Landscape, Weather, Construction) method.✅ Pivoting: Leveraging multi-engine reverse image searches (Yandex, …
hishing Attack Investigation – Cybersecurity Case Study Overview This project documents a real-world style phishing attack investigation conducted for educational and defensive cybersecurity purposes. The objective was to analyze a suspicious email, identify malicious infrastructure, and map the attack using …
Cybersecurity-Lab-AWS Step-by-step guide to building an AWS-based cybersecurity lab for hands-on learning and practice. I recently built my own AWS-based Cybersecurity Lab from scratch and documented the entire journey step by step. This lab is designed to simulate real-world …