OSINT HUB
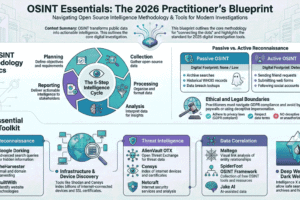
What is OSINT?
Start with a hook. OSINT isn’t just “Googling”; it’s the art of gathering data from publicly available sources to create actionable intelligence.
Key Concept: It’s used by journalists, cybersecurity researchers, and investigators to find the truth behind the noise.
The OSINT Lifecycle (The Process)
Explain that it’s not just about tools, but a process:
- Preparation: Defining what you need to find.
- Collection: Using tools to gather data.
- Analysis: Connecting the dots between different pieces of info.
- Reporting: Presenting the final findings.
The Essential Toolkit (The “Hub”)
Break down the tools by category so your readers can follow along:
- Search Engine Dorking: Using advanced operators (e.g., filetype:pdf or site:example.com) to find hidden files.
- Social Media Intelligence (SOCMINT): Tools for analyzing profiles and hidden connections.
- Image & Video Forensics: Reverse image searching (Yandex, Bing, TinEye) and metadata (EXIF) analysis to find where/when a photo was taken.
- Geospatial Intelligence (GEOINT): Using Google Earth and street-view mapping to verify locations.
Why It Matters for Cybersecurity
- For Businesses: Finding leaked credentials or sensitive data before hackers do.
- For Individuals: Understanding your “Digital Footprint” and how much of your life is exposed online.
Conclusion: Zero Fluff, Total Accuracy
Wrap up by emphasizing that while the tools are powerful, the mindset of the investigator is what matters most.
Complete Toolkit Guide Visit 👉 https://rahmymohamed.github.io/OSINT-HUB/