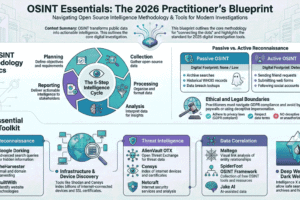
Top OSINT Tools for Cyber Security Students 🔍💻
Abstract
Open-Source Intelligence (OSINT) has become a fundamental component of modern cybersecurity investigations. This article presents a structured overview of ten widely used OSINT tools and examines their relevance for cybersecurity students. The study emphasizes responsible usage, analytical development, and practical application within legal and ethical boundaries ⚖️.
—
Introduction
In the contemporary digital environment, cybersecurity plays a critical role in safeguarding information systems, networks, and user data 🔐. As cyber threats continue to evolve, professionals increasingly rely on intelligence-gathering techniques to identify vulnerabilities and assess risks.
Open-Source Intelligence (OSINT) refers to the systematic collection and analysis of publicly accessible information from sources such as websites, public databases, search engines, and social media platforms 🌐. When applied ethically, OSINT supports threat analysis, digital forensics, reconnaissance, and security research.
For students pursuing cybersecurity education, understanding OSINT tools is essential for developing investigative and analytical competencies.
—
Significance of OSINT in Cyber Security Education 🎓
The study of OSINT tools contributes to:
- The development of structured research and analytical skills
- Awareness of digital exposure and online footprints
- Practical understanding of reconnaissance methodologies
- Strengthening ethical hacking and defensive security practices
Academic exposure to these tools enables students to connect theoretical knowledge with practical cybersecurity scenarios.
—
Top 10 OSINT Tools 🛠
- Shodan
- Maltego
- theHarvester
- Recon-ng
- SpiderFoot
- OSINT Framework
- Have I Been Pwned
- Censys
- FOCA
- Google Dorking Techniques
Each of these tools serves specific investigative functions, including device discovery, domain intelligence gathering, metadata extraction, breach identification, and network reconnaissance. These tools must be used strictly within ethical and legal frameworks ⚖️.
—
Reference Blogs 🔗
A detailed explanation and structured discussion of these tools are available on the following GitHub pages:
- Blog 01:
https://mushrifa-muzammil.github.io/cyber_security_OSINT_Blog01/ - Blog 02:
https://mushrifa-muzammil.github.io/cyber_security_OSINT_Blog02/
—
Conclusion 🌍
OSINT remains an essential discipline within cybersecurity research and practice. By gaining structured knowledge of OSINT tools and applying them responsibly, students can enhance their technical expertise and contribute meaningfully to digital security initiatives.
— MushrifaMuzammil